Security in the ‘Software Development Life Cycle’ needs a change of mindset; taking a ‘developer-first’ mentality to cyber security & an integrated end-to-end security model.
DevSecOps
We hacked DevOps… the people, the process and the technology; We built it as a service to help solve your development challenges. Let’s put the ‘Sec’ into DevOps, not by shifting left, but through frictionless engagement, tackling the heart of the process and security ownership, together. Lets see how…
Some Fundamental Questions
-
Have your Dev team lost trust in security or not getting the enablement they recognise they need?
-
Are the Dev teams missing security context to fix issues and buried in noise & extensive Issue Backlogs?
-
Do you have a cyclical DevSecOps process in place and do you continually iterate?
-
Can we save time and money in the process and eliminate expensive, unproductive automation and tooling?
DevSecOps
A significant opportunity
We all know that Pen Testing sits in the righthand side of the DevSecOps model, in the reactive, non-context based aspect of your SDLC. Rarely do testers interact with coders, the architects who designed your solution, and rarely do they have a true context or understanding of how a solution is built.
Together we need to resolve who owns security.
Is it security, operations, or does it rest with the developers? We also need to resolve the ambiguity that so many developers face on a daily basis with respect to security.
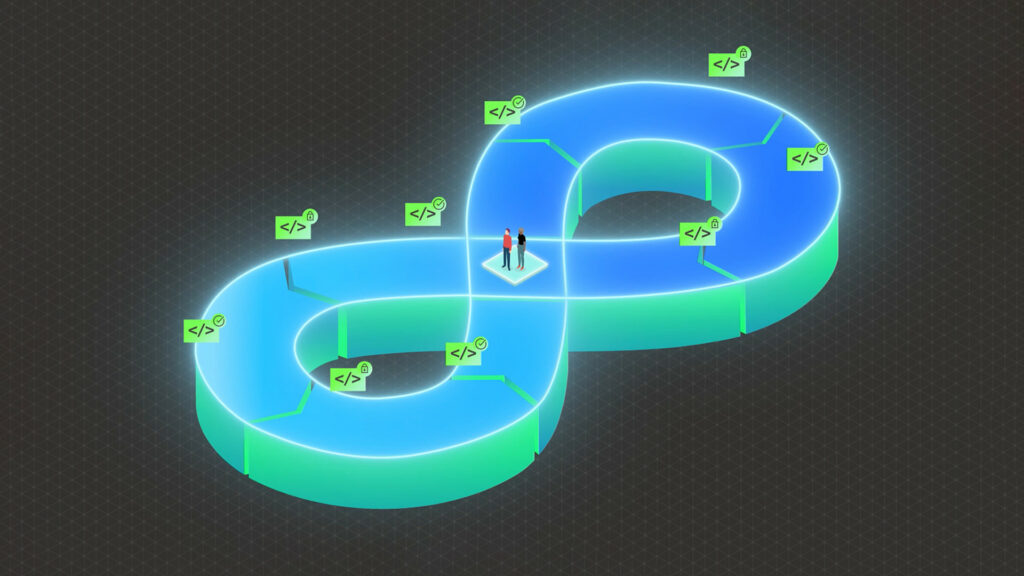
To understand the challenge in more detail, let's look together at a typical DevSecOps cycle, noting the proactive and reactive nature of each side of the equation.
A typical DevSecOps cycle
1. Plan
This is very early in the process and the ideal time for security to become involved.
- Develop threat model; the ‘evil story’
- Examine existing backlog and processes - fix problem creation at outset.
- Opportunity for early feedback, increased awareness and ownership.
2. Build
There are large volumes of code, significant noise and low trust in code review tools due to false positives.
- Work to tune existing toolsets to lean the cyber aspects of your toolchain, to produce valuable output and set in place processes for validation.
- Set an acceptable risk level for release.
- Educate and work with the development team to validate.
3. Test
Our first opportunity to test in a living environment, and examine how code, libraries, applications, containers, and integrations truly interact and behave together.
- Here we use DAST to find vulnerabilities and defects approved libraries
- We don’t forget containerisation at this stage.
4. Deploy
Code, containers and integrations are deployed, and we must accept a late lifecycle interception point.
- First stage to undertake Pen Testing which has limited context.
- Introduce security into your change management process.
- Validate integration with SIEM, WAF configuration and tuning; and put vulnerability management in place.
5. Operate
The production phase: the realm of business as usual, observation and normal operations./p>
6. Monitor
Pen Testing looks only at, and partially, the ‘technology’ in the ‘People, Process, Technology’ stack.
- Even when flaws are found, it’s not common to have access to the development team.
Let's rewind and visit some history
DevSecOps has become a buzz term that can mean so many things but in essence is a development methodology. In principle, it’s all about putting security into the DevOps process.
This does not mean turning on scanners and generating noise. For Chaleit it’s all about the process, setting a bar of materiality and taking a real-world, practical perspective to solving this challenge.
It also requires understanding the culture of your team and recognition of the challenges your developers face in their time-restricted sprints (which are delivery and feature focussed). Instead, we need to tailor programmes to orchestrate scale, streamline, create repeatability and to drive acceleration.
Challenging convention for a better outcome
Chaleit DevSecOps engineering is designed to take a software engineering perspective to the challenging problem of securing code in your pipeline.
It’s not a single piece of consultancy, a code review or a ‘shift left’ approach. Instead, we engage as an extension to your team to drive transformation and innovation into your release cycles on a continuous basis.
We drive accountability and ownership, and leverage DevSecOps platforms efficiently whilst resolving the big question of ‘who owns security’? We also removed the concepts of endless code reviews, sign-gates and other inhibitors. Recognising that Cyber Security should be an enabling function, we instead learn about your challenges, your agile process, sprints, tech-stacks and concerns about cyber risk.
Better Security Engineering Through Transformation
So how do we solve this together? How do we enable your teams, impose little overhead and drive the ‘Sec’ into DevSecOps? Let’s tackle this point by point:
DevOps
DevSecOps
-
1
Logic suggests working at the heart of where security flaws start; plan.
-
2
Identify, improve and enhance your processes with a focus on plan, build and code as quality.
-
3
Create an arrangement where we are there with you as the security ‘bridge’.
-
4
Reconsider Pen Testing as something within your cycle and not at the end with third parties.
-
5
Find better patterns, better bugs, understand the context and tune to reduce noise.
-
6
Eliminate the conflictual nature of external Pen Testers competing with your own team.
-
7
Ensure continuous access to resources to ensure no delay or red tape.
DevSecOps FAQ
It is not staffing, or augmentation. We become an extension to your team and journey together. We eliminate single points of failure and create scale: using our IP, know-how and experience bringing a disciplinary team to work together.
We are continuously there with you. Chaleit are an extension to your team and are as accessible as your internal teams. We aim to become a part of your team to give you eyes and ears at all stages, not just after a deployment.
We need to rethink and rewind. We need to ask ourselves, where do we start in the chain to create visibility? Ideally the best time is to solve never-ending issues lists by engaging at the plan stage and catch things in build.
Chaleit’s goal is to help you start at the beginning of the process, create scale, and join all the testing dots together.
This is wonderful as it gives us a starting place. We work with clients at all levels of enterprise and maturity, including those with:
- CI/CD pipeline already established - we work directly with the Devs and connect with their culture to create scale and plug the skills gap.
- Large backlogs / Issues - we work to refine, tune and educate, by joining all your processes up and redefining what's important to you.
- Under-resourced or no Sec Team - no problem; we bring these skills as a service to you to create scale and bridge the knowledge gap.
We challenge traditional thinking about upstream ‘point in time audits / Pen Tests’. They have no context, use static reports, no knowledge base and do not interface to the business or developer community (who in turn, have no visibility into issues boards and the development process).
Pen Tests examine a limited surface of a deployment and generally have a restricted scope. This is becoming a major issue with complex integrations, containerisation, rapid deployments and continuous sprints.
"Pen Testing is a valuable exercise, but it becomes involved late in the lifecycle. It is also technology centric in the ‘People, Process, Technology’ stack and thus lacks context, instead becoming a bite-sized audit at a point in time.
Perhaps it’s time to consider Pen Testing as just another tool in the toolchain and your lifecycle, and recognise that error can be engineered out at source, and flaws caught much earlier in the process.
Our work often ends up with us working directly with your supply chain as well. When you have third party teams in your lifecycle, they often become the weak point and are generally driven by features and releases rather than code quality from a security perspective. We work with a number of clients to address this challenge to drive code quality together.
They certainly are, but like all tooling they can be expensive, noisy, lack context and require constant refinement, integration, adoption and tuning, which can be complex and time consuming; often not leading to a net increase in visibility and security.
Whilst scanning tools integrate automatically into issues boards, they create great volume, noise and vast amounts of false positives. They worryingly also have false negatives.
Chaleit Cyber Digital Protection addresses the upstream skills gap and accessibility to Cyber Security skills, and provides this ‘as a service’ on a continuous basis. It eliminates the need for the third party Pen Testing issues outlined above, and is valuable for teams with a wide engagement. Chaleit DevSecOps Engineering is driven from right within the heart of your code factory and interfaces with Cyber Digital Protection. We offer packages that offer total flexibility in blending these very different skill sets.
Cyber Digital Protection
Learn how we can add value to your company with our Cyber Digital Protection offering and how it could work for you.