Our approach considers and adapts to such complexities and errors that occur with the ease of deployment and scale that gives cloud its advantage.
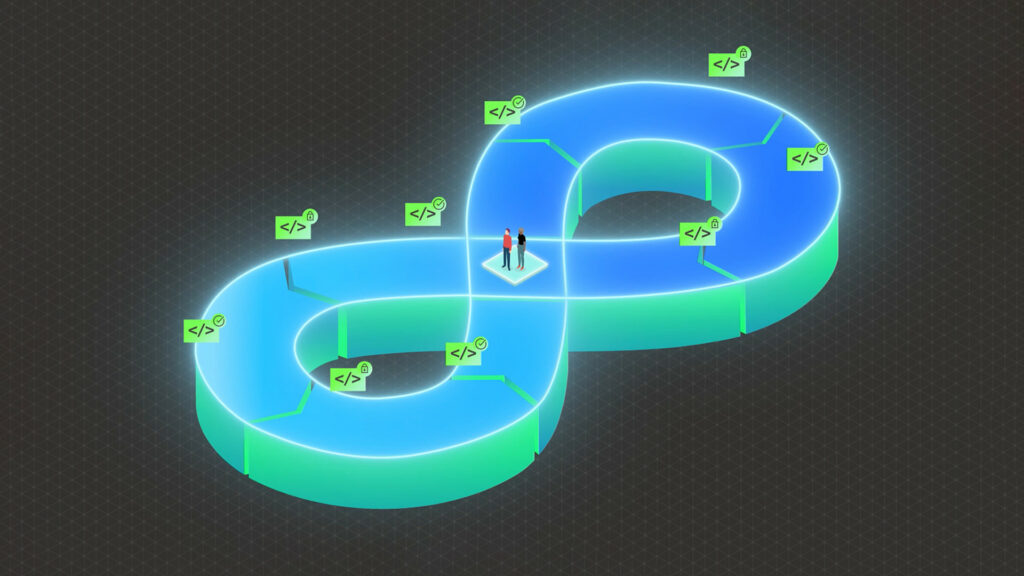
A New Realm of Risk: Cloud services come with so many new dimensions of risk. Where the components of an overall environment may span traditional Infrastructure and some Cloud components for specific tasks (hybrid Cloud) to full use of Cloud for both Applications and Infrastructure (and everything in-between). Unlike a contained application, the boundary of security controls and flow does not start and end with defined borders, nor can we sit it within our own DMZ and apply traditional management and monitoring to it.
Security weaknesses in the cloud itself are not the scope of review or work in this instance. Our capabilities lead us to assess the integration and the hand-off/delineation of responsibility and service and uniqueness of design in infrastructure, applications, data and integrations of an overall environment.
Beyond Basic Cloud Methodology: In terms of methodology, we use best practice plus our own methods. The Cloud Penetration Testing Handbook provides a good basis for the high-level work and approach for testing but like all great frameworks this forms the basis for expert work and this is where expertise, workflow and IP are required on top of such methods.
It is key to examine and validate the myriad of components, micro services, data flows, hand-offs of responsibility, layers of IaaS (Infrastructure as a Service), PaaS (Platform as a Service) and SaaS (Software as a Service) that give rise to so much opportunity for flaws to be expressed and inherent vulnerabilities to be exploited.